
Invest in IndieBio Companies

Companies Raising Now
Every season of the year, a new batch and about one-sixth of our alumni are in raise mode. The companies above are currently raising and would love to talk to interested investors. We can set up those meetings or you can contact the companies directly.

Don’t wait for Demo Day!
We encourage our startups to meet with investors during our programs. We announce our new startups a month into the program, and for the next 100 days we expose them in many ways – from 1:1 meetings, pitch practice days, and investor speed dates. A majority of our startups have soft-pencilled full rounds prior to Demo Day. Let us know if you are interested!
Investing with SOSV
IndieBio / SOSV shares a cap table with over 430 funds for the IndieBio portfolio alone. SOSV’s complete network is far larger. Lets us know if you would like to know more about investing with SOSV in biotech, hard tech and Asia cross-border. We love to meet new VCs.

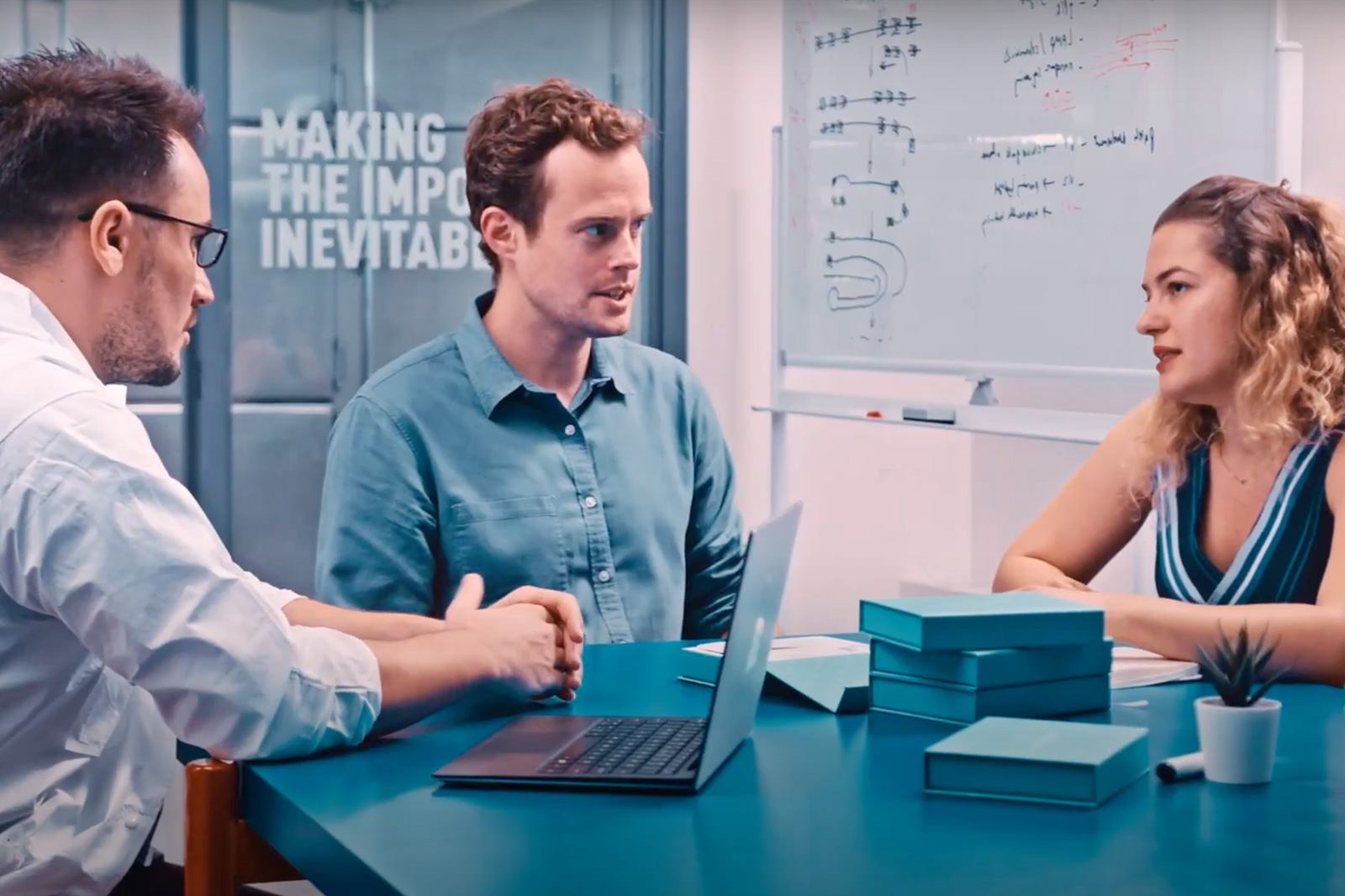
Backing Life Science Founders
The SOSV Consortium consists of investment entities that originated at SOSV and in which SOSV is an anchor limited partner and remain closely aligned with SOSV.
You are in Good Company
430+
$1.2B
$8.3B+







Corporate Partners
We work with hundreds of global corporates, and their CVCs, and we are open to anyone who has innovation onramps designed to facilitate rapid experimentation. We welcome site visits and will take great care of you. Our top priority is speed, but trust is a prerequisite. Every successful IndieBio alumni has great relationships with corporate partners, be they an investor, a supplier, a manufacturer, or a customer.
What works well:
Master-MTAs, standardized two-ways NDAs, no-rights experiments/trials, pilot projects, CVCs with dry powder, and access to real decision-makers, not just gatekeepers.
What doesn’t work:
Exclusivity without upfronts, multi-level decision making, specialized agreements that take extensive legal review to start work, and in-house champions who don’t have bandwidth for new projects.

Newsletter Signup
We don’t spam. Our Privacy Policy and Cookie Policy apply. The site is protected by reCAPTCHA.